Metro/High-Speed Rail Onboard Firewall, M12 Interface Firewall Solutions
Industry Solutions — Integrated Monitoring System
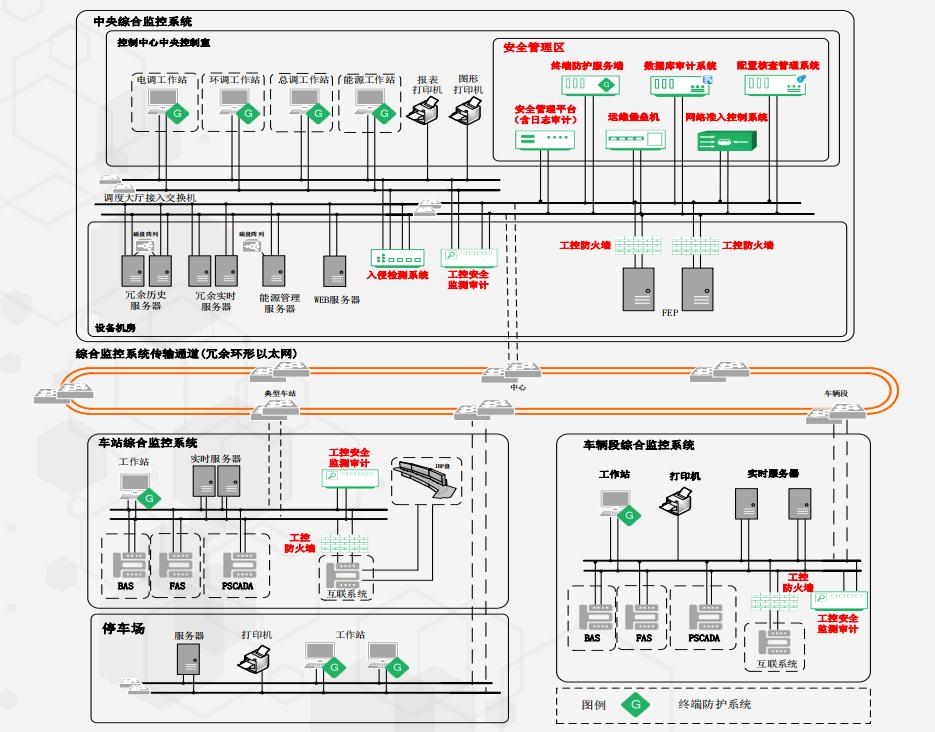
- Communication Network Security
Monitoring and Auditing: Passively deploy an Industrial Control Security Monitoring and Auditing System on switches at stations, depots, parking lots, control centers, backup centers, and equipment maintenance centers. This system collects, analyzes, and processes network traffic, and in conjunction with specific security policies, provides real-time alerts for abnormal operations and attacks, and conducts post-event auditing.
Intrusion Detection: Passively deploy an Intrusion Detection System to extract features from traffic and match them against a rule base, quickly and effectively identifying anomalies and attack behaviors in industrial control networks.
- Zone Boundary Security
Boundary Protection: Redundantly deploy industrial control firewalls between stations, depots, parking lots, control centers, backup centers, and interconnected system interfaces to achieve zone boundary protection.
- Computing Environment Security
O&M Management and Control: Deploy an O&M bastion host in the control center or depot to achieve comprehensive auditing and behavior control for remote O&M operations, meeting remote O&M management and control requirements.
Endpoint Protection: Deploy endpoint protection system clients on operator and engineer workstations to achieve endpoint security hardening, process whitelist control, and USB removable media control.
Database Auditing: Deploy a database auditing system in the management center to detect and audit database usage, effectively identifying abnormal database access behaviors.
- Security Management Center
Security Management Platform: Deploy a Security Management Platform (including log auditing) in the control center to perform normalized collection and correlation analysis of logs and alerts from security devices, network devices, and host devices, displaying the security posture and warnings, thereby comprehensively improving security protection efficiency and security management capabilities.
Industry Solutions — Signaling System
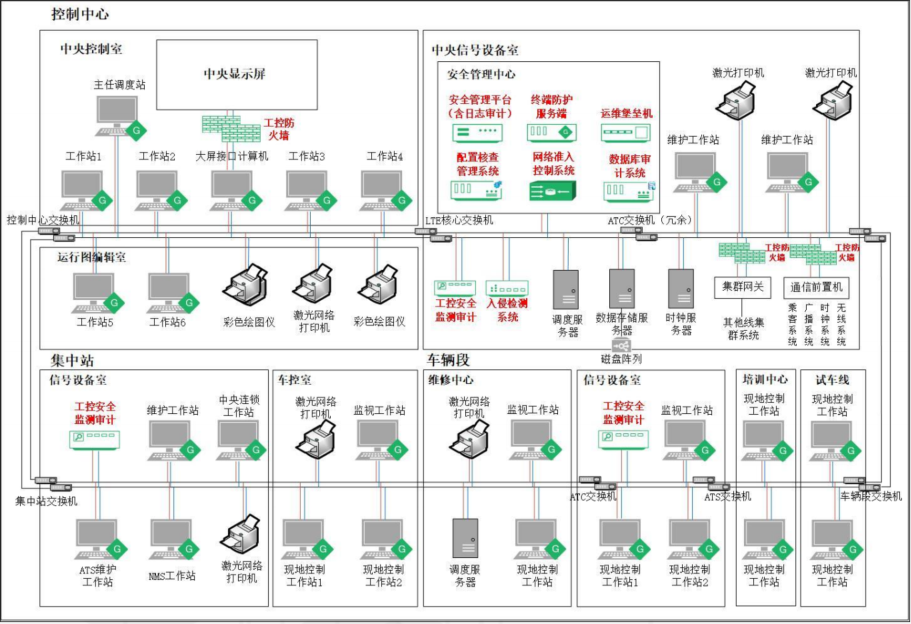
- Communication Network Security
Intrusion Prevention, Monitoring and Auditing: Passively deploy an Intrusion Detection System on switches at the control center and centralized stations to perform field-level parsing of network traffic, establish protocol baselines, traffic baselines, and link baselines, and provide real-time alerts and post-event auditing for abnormal operations, illegal intrusions, malicious code execution, and other behaviors.
- Zone Boundary Security
Boundary Protection: Redundantly deploy firewalls between the control center and interconnected system interfaces to achieve zone boundary protection.
- Computing Environment Security
O&M Management and Control: Deploy an O&M bastion host in the control center to achieve comprehensive auditing and behavior control for remote O&M operations, meeting remote O&M management and control requirements.
Malware Prevention: Deploy endpoint protection system clients (which can also be deployed standalone) on operator workstations, engineer workstations, and servers to achieve endpoint security hardening and USB removable media control.
- Security Management Center
Security Management Center: Deploy a Security Management Platform in the control center to perform normalized collection and correlation analysis of logs and alerts from security devices, network devices, and host devices, displaying the security posture and warnings, thereby comprehensively improving security protection efficiency and security management capabilities.
Industry Solutions — Onboard Communication System
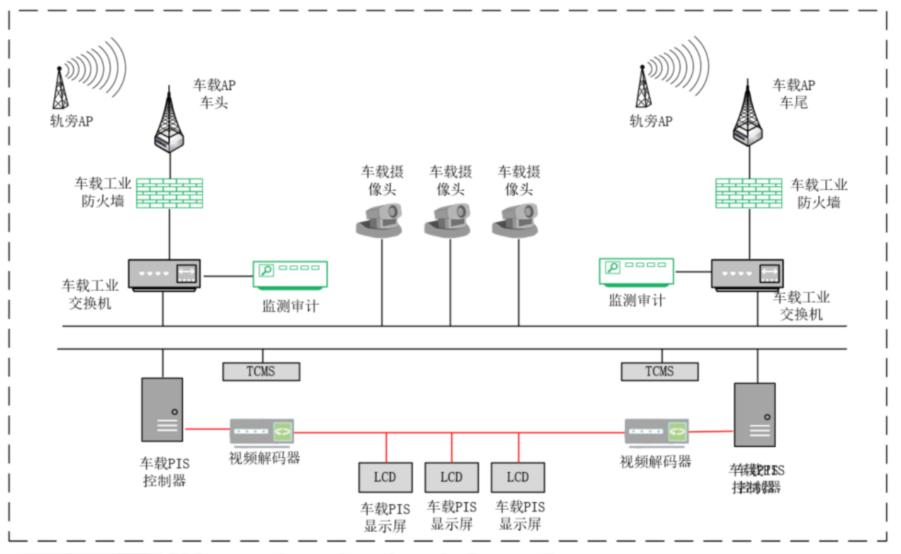
- Train-to-Ground Wireless Communication Boundary Protection
By deploying onboard firewalls at both the head and tail of the train, policy control is applied to train-to-ground communication traffic, effectively reducing the spread of network storms, attack behaviors, and viruses from ground business systems to the train.
- Logical Isolation Between Multiple Services Carried by Train-to-Ground Wireless
Although wireless transmission systems can achieve a certain degree of logical isolation through technologies like VLANs, an analysis of the prevention and control requirements for secure communication networks and secure zone boundaries indicates the need to deploy firewall devices with more effective security control to achieve logical isolation between different services.
- Real-time Alerts and Post-Event Auditing
The onboard industrial firewall can push its alert information, audit information, and log information in real-time to the ground security management center of the communication system via interfaces such as SysLog and SNMP. This enables security O&M management functions including pre-event warning, real-time alerting, and post-event auditing, thereby enhancing the emergency response and control capabilities for metro network security.