Fully Domestic FeiTeng + FPGA Architecture with B-Code Support, 12 Ethernet Ports, and Multi-Serial Power Communication Management Solution
Industry Pain Points:
China's power grid has become the most extensive and structurally complex man-made technological system in the world today. With the introduction of a series of laws and regulations by national ministries and commissions—such as the Cybersecurity Law of the People's Republic of China, the Guidelines for Information Security Protection of Industrial Control Systems issued by the Ministry of Industry and Information Technology, Order No. 14 from the National Development and Reform Commission titled Regulations on Security Protection for Power Monitoring Systems, and the Notice on Issuing Overall Security Protection Schemes and Evaluation Standards for Power Monitoring Systems issued by the National Energy Administration—the importance of cybersecurity protection in the power industry has been significantly emphasized. Driven by the urgent need for domestic substitution of IT infrastructure in the power sector, as well as the proposal and implementation of initiatives such as "Smart Power Plants" and "Strong Smart Grids," there is an increasing demand for intelligent, networked, high-performance, and integrated solutions for secondary power equipment.
In accordance with relevant standards such as the Technical Specification for Substation Data Communication Gateway, our company has developed hardware products based on FeiTeng CPUs and Tsinghua Unigroup FPGAs. These products meet the requirements for communication management units, gateway devices, intelligent remote terminals, online monitoring systems, network analysis and recording instruments, and other secondary equipment used in the power industry. The localization rate of these products reaches 95%, and can be customized up to 100% domestic component usage upon customer request. The products support domestically developed operating systems such as NeoKylin.
Solution Overview:
Secondary power equipment refers to low-voltage devices used to monitor, control, measure, regulate, and protect primary equipment. This includes measuring instruments, control and signaling devices, relay protection devices, automatic remote control systems, operation power supplies, control cables, fuses, and more. The construction of secondary power equipment must comply with cybersecurity classification protection requirements and the overall security protection requirements for power monitoring systems set forth by the National Energy Administration. Following the principles of "security autonomy, intelligent control, horizontal isolation, and vertical authentication," the deployment of secondary equipment should be implemented from four perspectives: entity, structure, behavior, and management.
Currently, FeiTeng, together with major domestic manufacturers of secondary equipment and information security products, has jointly proposed a comprehensive solution for networking, transmission, information interaction, and information security protection for intelligent secondary equipment in the power sector, as illustrated below:
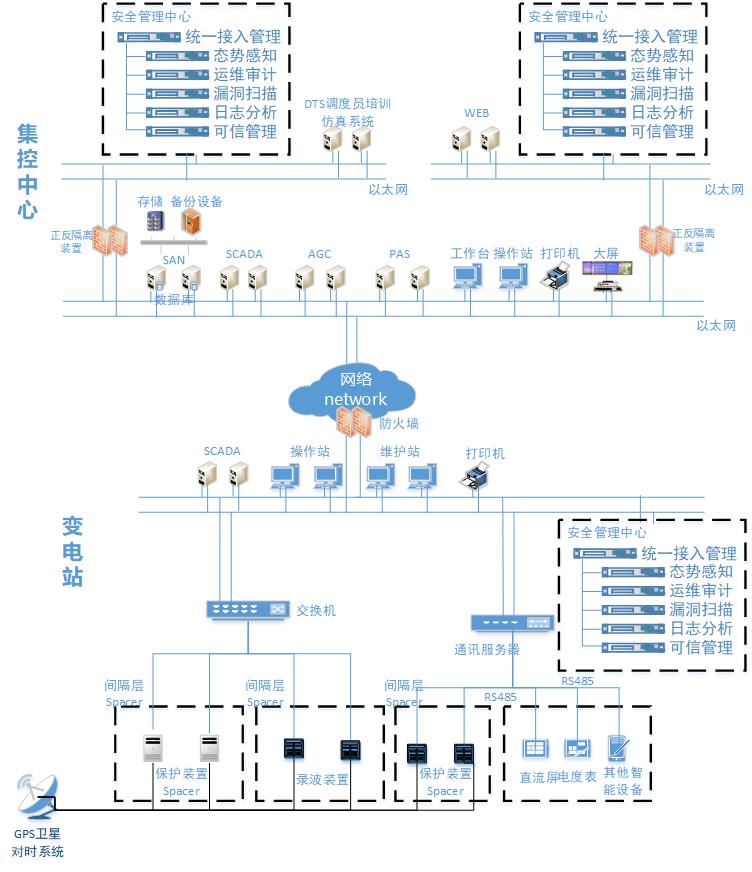
Functional descriptions of each component are as follows:
Relay Protection Device: Intelligent industrial products based on FeiTeng CPUs launched by leading domestic secondary equipment vendors, capable of effectively implementing communication, early warning, and automatic protection command functions for relay protection devices.
Fault Recording System: A fault recording system based on FeiTeng CPUs that can accurately record waveforms and effective values of three-phase currents, zero-sequence currents, three-phase voltages, and zero-sequence voltages during fault events. It generates detailed fault analysis reports, identifies fault types, and allows users to view amplitude and phase of current and voltage, local protection operation timing, transmit/receive timing of high-frequency protection transceivers on both sides of the line, and circuit breaker open/close times.
TTU Product: FeiTeng CPU-based TTUs effectively support information acquisition and control for distribution transformers.
Communication Management Unit (Communication Server): Connects to relay protection and fault recording devices, converting their proprietary communication protocols into Ethernet protocols.

Host Protection System: Security software deployed on upper-level workstations and FeiTeng CPU-based servers to enhance system security, patch vulnerabilities, eliminate viruses or malware, and prevent malicious software from spreading via USB drives or other mobile media. It reports security events such as changes in hardware/software configurations and failed password attempts.
Firewall: A boundary isolation and security protection product designed specifically for industrial control systems. It can be deployed in front of critical DCS, PLC, and SCADA systems. In addition to standard firewall capabilities such as access control, auditing, VPN, and DoS attack protection, it supports mainstream industrial protocols including OPC, Modbus TCP, S7, IEC104, and EIP, enabling isolation between zones of different security levels. Built on an industrial-grade hardware platform, it features wide temperature tolerance, electromagnetic interference resistance, and adaptability to harsh environments, ensuring robust protection for both itself and the systems it protects. The firewall product has already been adapted to run on FeiTeng CPU-based servers.
Switch: An industrial environment–compatible switch used to connect devices within the same security zone. It includes built-in firewall functionality, access control, hardened operating system for self-protection, packet filtering, MAC binding, and other features to enhance network security. It also supports SNMP, logging, and port mirroring to facilitate monitoring and auditing by other security devices.
Intrusion Detection System (IDS): Typically deployed alongside switches in a one-to-one configuration using passive monitoring, which does not interfere with existing services. It analyzes network traffic to detect anomalies and attack behaviors. During an attack, it can coordinate with switches and firewalls to block malicious connections and preserve evidence. Detection thresholds can be automatically adjusted through self-learning. It also provides traffic pattern and distribution statistics for the local area network, helping administrators understand the security landscape. Secondary equipment manufacturers have already released FeiTeng-based switches and intrusion detection devices.

Network Diode (Unidirectional Gateway): Based on FeiTeng CPUs, this device contains two host modules connected to internal and external networks respectively. There is no direct connection between the two modules; only limited protocols such as file transfer, database access, and video streaming are supported. Data is transferred as pure data blocks "ferried" between the two modules, ensuring that attack packets and unauthorized connections cannot pass through. It also supports standard firewall functions such as access control, attack defense, and content filtering.
Trusted Terminal: Refers to desktops, servers, network security devices, and industrial control devices based on FeiTeng CPUs. In addition to their original functions, these terminals integrate trusted computing modules within the CPU to ensure that critical hardware, BIOS, and operating systems cannot be tampered with. During operation, they continuously monitor device security status and report it to the management platform, enabling dynamic adjustment of protection strategies. This adds a robust protective layer directly to the device.
Unified Security Management: Centralizes the management of security products and events across the network. Managed devices include boundary isolation systems, network monitoring tools, host protection systems, intrusion detection systems, and operation/maintenance management systems. It enables unified configuration of security policies, comprehensive monitoring of operational status, and real-time alerts for security incidents, helping users understand overall network security posture and reduce operational costs.

Trusted Management Platform: Manages trusted terminals across the system, collecting operational data from each node and performing correlation analysis to detect and alert on attack behaviors. Security policies can be uniformly distributed and dynamically learned and adjusted. By organizing trusted terminals into a coordinated network, it enhances the flexibility and effectiveness of defense mechanisms.
Vulnerability Scanner: Also known as "threat detection" or "security compliance analysis," this tool periodically scans common SCADA systems, configuration software, HMIs, PLCs, DCSs, application systems, and databases. Using rule sets and multiple scanning techniques, it identifies vulnerabilities and weaknesses, detects non-compliance with policy requirements, and provides remediation recommendations. Additionally, with a comprehensive device fingerprint database, it collects device information during scans to assist in asset management.
Operation and Maintenance Audit: Addresses challenges such as complex login methods, hard-to-remember passwords, and difficulty tracing operations. This device provides a single sign-on interface with simplified authentication (e.g., mobile QR code scanning, fingerprint recognition), allowing O&M personnel to operate internal network devices through a centralized system. It includes fine-grained permission management, records all operations (with playback capability), and triggers alerts for policy violations.
Situational Awareness: By deploying probe applications at various points across the network, it aggregates data on traffic volume, direction, and type to a central management center. Using big data analytics, it evaluates network load and health conditions, detects trends in cyber threats, and displays these risks and trends in real time via visual dashboards, enabling administrators to clearly understand the overall network status.
Log Analysis: Collects and centrally analyzes logs from various systems to understand device operation status, identify security incidents, and improve overall system protection. It also provides historical log querying and real-time security alerting capabilities.
The integration of the above components forms the ecosystem core for the construction and use of secondary power equipment. This ecosystem is interconnected via industrial switches, dedicated firewalls, and other network devices. Featuring high intelligence, high integration, and strong service processing capabilities, it meets the requirements for secure autonomy, intelligent control, horizontal isolation, and vertical authentication in power industrial control equipment and systems—ensuring continued safe and normal operation even when the business network is under attack.